"Phishermen’s" Latest Exploited Brand — Adobe
October 2019 by Patrick LEBRETON
Cybercriminals leverage trusted domain’s redirect link services to cast phishing nets
Cybercriminals love serving up phishing attacks to unsuspecting users through links that appear trustworthy, and their latest attack vector is Adobe redirect services. Adobe and Google both offer open services that allow users and their organizations to create customized links, including trusted domain names. Unfortunately, this service is also available to cyberattackers to exploit.
These "phishermen" use those web links, masked with trusted domain names (such as Google, Microsoft, and now Adobe) to lure users to click on these redirect links which send the users to phishing web pages.
SlashNext threat researchers found that these cyber attackers are abusing Adobe’s open redirect services, which are hosted at t-info[.]mail[.]adobe.com. These phishing links direct the user to login pages such as this one which mimics a Microsoft account page:
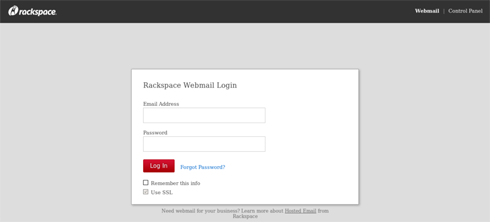
Unfortunately, users click on these seemingly trustworthy links that redirect them to various malicious sites, often requesting credentials (email addresses, passwords, etc.) to what they think are legitimate account login pages. Threat researchers found that these links, which feigned an Adobe source, directed users to several different pages such as the Microsoft one as well as this one which directs to major cloud computing company Rackspace.
"This specific method of phishing is particularly challenging to defend against because of how quickly cyber attackers can change the redirects to send victims to several different phishing pages," Mushtaq said. "Hackers can rapidly alter and create new malicious web phishing pages that steal user credentials."
Redirect links are easily customizable, and many users access common brands such as Google and Microsoft so often that they click on phishing links without realizing they are falling right into the attackers’ net. Despite that 79 percent of people say they can distinguish a phishing message from a real one (according to a recent report from Webroot), almost half (49%) admit to clicking on a link from an unknown source — while at work. This means they have potentially exposed themselves to phishing attacks that can exploit user credentials to infiltrate companies’ internal systems and access critical information.
"Stealing credentials is one of the top ways for cybercriminals to gain access to organizations’ networks to steal sensitive data," said Joseph Carson, chief security scientist at Thycotic. "User credentials are a main target because they are the foot in the door that allows the attacker to discover ways to bypass security."
Targeting credentials is a go-to strategy for attackers because once the user’s accounts are compromised, attackers have the same power as the authorized user. Cybercriminals typically steal these privileged credentials using social engineering tactics through various email and browser-based phishing techniques. Once inside organizations’ accounts (gained from the users stolen credentials), these criminals are able to conduct data exfiltration, disrupt processes or even lay the foundation for a larger-scale attack — all from just tricking a user into clicking onto a phishing link by masking it as a trusted source.
"These attacks are on the rise and manipulating mainstream trusted brands is a favorite tactic of online criminals," said Atif Mushtaq, CEO of SlashNext. "These ploys are becoming more prevalent because they are challenging to detect and they evade existing URL inspection and domain reputation analysis methods."







 Actu
Actu